Expressvpn Glossary
User Datagram Protocol (UDP)

What is a User Datagram Protocol?
The User Datagram Protocol (UDP) is a transport-layer communication protocol that sends data packets (datagrams) between devices without establishing a connection. Its core purpose is to provide simple, low-overhead message delivery when minimizing latency and protocol complexity is more important than guaranteed delivery.
Unlike the Transmission Control Protocol (TCP), UDP uses best-effort delivery and doesn't confirm whether data arrives safely, arrives in order, or arrives at all. At the UDP layer, it doesn't use a handshake or maintain connection state between endpoints.
How does the User Datagram Protocol work?
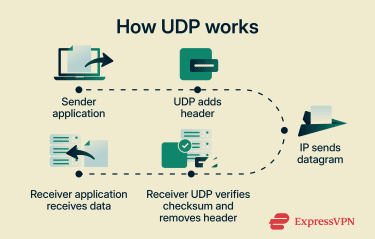
- An application sends data to the operating system’s UDP layer, specifying a destination IP address and port number.
- UDP adds header fields to the data: source port, destination port, datagram length, and a checksum for basic error detection. The checksum is mandatory in IPv6 and optional in IPv4.
- The completed datagram is passed to the IP layer, which routes it toward the destination IP address. Each datagram may take a different path because routing decisions are made independently.
- At the destination, the IP layer delivers the datagram to the UDP layer.
- UDP checks the checksum (if present) to detect corruption and discards invalid packets.
- If the packet is valid, UDP delivers the payload to the application bound to the destination port.
- If datagrams are missing, duplicated, or out of order, UDP doesn't correct these conditions; handling is left to the receiving application (if needed).
Where is the User Datagram Protocol used?
Common uses include:
- Real-time communication and media: Voice calls, video calls, live streaming, and Voice over Internet Protocol (VoIP) often use UDP to reduce delay. Some packet loss can affect quality, but avoiding retransmission delays can keep playback smoother in real time.
- Real-time interactive apps: Online gaming and real-time telemetry, such as remote sensors, GPS trackers, and some Internet of Things (IoT) devices, use UDP for frequent, time-sensitive updates, such as position changes, sensor readings, and status messages.
- Core internet infrastructure: Services such as Domain Name System (DNS) queries and responses, and Network Time Protocol (NTP) synchronization often use UDP for fast, lightweight exchanges without connection setup.
- Some modern web and networking protocols: HTTP/3 and some virtual private network (VPN) tunneling protocols, run over UDP to support low-latency transport and improve responsiveness, especially on unstable or congested networks.
Why is the User Datagram Protocol important?
UDP is important because its low overhead and connectionless design support time-sensitive communication and high-volume network traffic. It enables data exchange to start without connection setup delays, which helps real-time and interactive applications remain responsive even when some packets are lost or arrive out of order.
UDP is also important as a transport foundation for protocols that add performance and reliability features on top of UDP, such as Quick UDP Internet Connections (QUIC). This supports modern web traffic by enabling low-latency connection establishment and improved connection resilience, including during network changes such as switching between Wi-Fi and mobile data.
UDP also works with IP multicast and, in IPv4 networks, can be used with broadcast communication, in which a single packet can be delivered to multiple receivers. This is useful for distributing updates within networks. In constrained environments, reduced protocol overhead can lower processing and transmission costs compared with connection-oriented approaches, though applications using UDP still need to handle congestion and any required reliability appropriately.
Risks and privacy concerns
UDP doesn't provide built-in confidentiality, authentication, or reliable delivery, which can create security and privacy risks when applications and services don't add protections at higher layers:
- Source spoofing and reflection attacks: UDP doesn't verify the sender’s address, which can allow attackers to spoof the source IP and cause servers to respond to a victim.
- Amplification from exposed or misconfigured services: Some UDP-based services can generate responses much larger than their requests, which can be abused to amplify traffic sent to a target.
- UDP floods and bandwidth exhaustion: Large volumes of UDP traffic can be used in denial-of-service (DoS) attacks that overwhelm network capacity and disrupt legitimate traffic. Because UDP has no inherent congestion control, poorly designed UDP traffic can also worsen congestion.
- Scanning exposed UDP ports: Unlike TCP, UDP has no handshake, so scanners typically must send protocol-specific probes and interpret any replies; the absence of a response is inconclusive and often treated as open or filtered rather than definitely open. Responsive UDP services can still be discovered or fingerprinted, increasing attack surface and enabling follow-on exploitation if vulnerabilities exist.
- Metadata exposure without encryption: If the application doesn't encrypt traffic, observers can often infer who is communicating with whom and when (from visible metadata such as IP addresses, timing, packet sizes, and sometimes port numbers), which can reveal usage patterns and activity.
Further reading
- TCP vs. UDP: Understanding the key differences and best use cases
- What are network protocols? A complete guide
- What is TCP/IP, and how does it work?
- What is OpenVPN, and how does it work?



