Expressvpn Glossary
Data Execution Prevention (DEP)

What is Data Execution Prevention?
Data Execution Prevention (DEP) is a security feature that helps prevent malicious code from running in protected areas of computer memory. It also helps protect systems from exploits that rely on running injected code through memory corruption vulnerabilities.
How does DEP work?
DEP works by marking specific areas of memory as non-executable. When a program attempts to execute code from memory regions marked as non-executable, the processor raises an access-violation exception. Unless the exception is handled, the operating system terminates the affected process.
Types of Data Execution Prevention
DEP can generally be implemented in two main ways: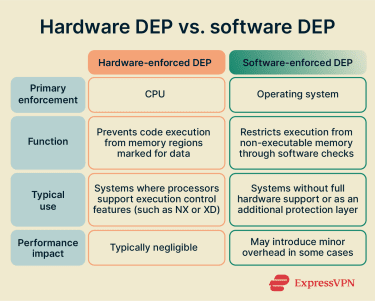
- Hardware-enforced DEP: Uses processor features such as the No-Execute (NX) or Execute Disable (XD) bit to mark memory pages as executable or non-executable. This approach provides stronger protection and is widely used in modern systems.
- Software-enforced DEP: Relies on operating system checks to detect unsafe execution behavior, particularly in older hardware environments that lack processor-level support or as an additional layer of exploit mitigation.
DEP implementation across platforms and environments
DEP is supported across most modern operating systems:
- Windows: DEP is built into modern Windows systems and is enabled by default in most configurations, helping protect applications and system processes from memory-based exploits.
- Linux and UNIX-like systems: Modern Linux kernels support non-executable memory protections using processor features such as the NX bit, which are enabled by default on most 64-bit systems. BSD and other Unix-like systems implement similar kernel-level protections by default.
- macOS (OS X): macOS enforces memory execution restrictions for applications and system components, preventing writable memory regions such as the stack and heap from executing code.
- Mobile (Android and iOS): Both Android and iOS enforce DEP at the kernel level; Android through Linux kernel memory protections, and iOS through ARM's Execute Never (XN) feature.
Risks and limitations
While DEP improves protection against memory-based exploits, it is not a complete security solution.
- Limited protection scope: Some exploitation techniques, such as code-reuse attacks, can avoid DEP by using existing executable instructions instead of injecting new code.
- Reduced coverage through exceptions: Application exemptions or system configuration changes may disable DEP in certain cases.
- Compatibility tradeoffs: Some legacy software that relies on dynamic code execution may not function correctly when DEP is enforced.
Further reading
- What is buffer overflow, and why is it dangerous
- What is a zero-day exploit? Everything you need to know
- Log4Shell vulnerability: What it is and how to stay protected
- How to protect your devices from bluesnarfing attacks
FAQ
Is DEP the same as the NX/XD bit?
On Windows, the operating system feature that uses this hardware support is called Data Execution Prevention (DEP). On Linux, the equivalent OS-level feature is also called the NX bit. So, depending on the platform and context, DEP, NX, and XD may refer to the same underlying protection implemented at different levels.

