Expressvpn Glossary
Elliptic curve cryptography (ECC)
What is ECC?
ECC is a type of public-key cryptography that uses the mathematics of elliptic curves to generate secure keys for encrypting data, sharing secrets, and digitally signing messages.
It achieves comparable security to older public-key systems such as Rivest-Shamir-Adleman (RSA) using smaller key sizes, which reduces computational and bandwidth requirements.
How ECC works
ECC uses math based on points on a predefined elliptic curve to create secure encryption keys.
The curve itself and a specific starting point on that curve, called the base point, are public parameters defined by cryptographic standards and enforced by the security protocol in use.
ECC’s security comes from a mathematical puzzle known as the elliptic curve discrete logarithm problem. Starting from the base point, it's easy to repeatedly “multiply” the point to reach another point on the curve. But working backward to figure out how many steps were taken is computationally infeasible. This one-way property is what makes ECC secure.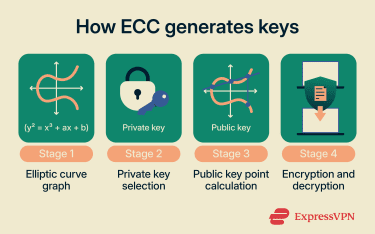
In practice, each side of a connection generates a private number and uses it to compute a corresponding public point on the curve. These public points can be shared openly. By combining their own private number with the other party’s public point, both sides independently derive the same shared secret, which is then used to encrypt data.
This mathematical property allows ECC to achieve comparable security to older public-key systems using smaller key sizes.
Characteristics of ECC
- Smaller key sizes: Achieves comparable security to older public-key systems using shorter key lengths.
- Computational efficiency: Smaller keys reduce processing and bandwidth requirements during cryptographic operations.
- Lower power and bandwidth use: ECC requires less computation and transmits less data during key exchange, making it suitable for mobile devices, IoT hardware, and battery-powered systems.
- Elliptic curve discrete logarithm basis: Security relies on the computational difficulty of the elliptic curve discrete logarithm problem.
- Support for key exchange and digital signatures: Used in cryptographic schemes such as Elliptic Curve Diffie-Hellman (ECDH) and Elliptic Curve Digital Signature Algorithm (ECDSA).
- Current standards adoption: Included in many modern security protocols and industry standards.
Security risks and vulnerabilities
- Curve choice: The security of ECC depends on the choice of elliptic curve parameters. Using curves that lack sufficient cryptographic strength or are improperly defined can introduce vulnerabilities.
- Implementation quality: Programming errors, including improper randomness generation or timing variations, can weaken security and expose private keys.
- Side-channel exposure: Observing timing, power consumption, or electromagnetic emissions may reveal information about secret keys if protections against side-channel attacks are not in place.
ECC vs. RSA
| ECC | RSA | |
| Key size | Shorter key lengths (e.g., 256 bits) | Longer key lengths (e.g., 3072 bits) |
| Speed and performance | Generally requires less processing and bandwidth | Generally requires more processing and bandwidth |
| Security basis | Based on the elliptic curve discrete logarithm problem | Based on the integer factorization problem |
Common uses of ECC
- Web encryption: Used in Transport Layer Security (TLS) to secure data between browsers and servers.
- Key exchange and digital signatures: Forms the basis of ECDH for key exchange and ECDSA for digital signatures.
- Mobile and embedded devices: Used in environments with limited processing power or memory due to smaller key sizes.
- IoT security: Applied to device authentication and encrypted communication in constrained hardware environments.
- Cryptocurrencies: Used for wallet key generation and transaction signing in systems such as Bitcoin and Ethereum.
- Government systems: Included in standards for securing sensitive communications.
Further reading: Blog articles
- What is cryptography?
- What is quantum cryptography?
- Lattice-based cryptography
- Post-quantum cryptography
FAQ
Why does ECC use smaller keys?
Where is ECC used in everyday technology?
What makes ECC efficient for mobile devices?
How does ECC protect against eavesdropping?
An observer can see the public data but cannot derive the secret without solving the elliptic curve discrete logarithm problem, which is computationally infeasible on secure curves. The shared secret is then used with symmetric encryption to encrypt transmitted data.


