Expressvpn Glossary
Hardware security module (HSM)

What is a hardware security module?
A hardware security module (HSM) is a physical computing device designed to securely generate, store, and manage cryptographic keys. An HSM often comes in the shape of a plug-in card or an external device that connects to a computer or physical server.
How a hardware security module (HSM) works
An HSM’s operation begins when an authorized application sends a request to generate a cryptographic key. The HSM generates cryptographic keys internally within its tamper-resistant hardware and stores them. The key never exists outside the HSM in plaintext form.
When the application later requests encryption, decryption, or digital signing, the HSM uses the stored key internally to perform the operation and returns only the result. Because the HSM creates, stores, and uses the keys itself, it controls the entire cryptographic key lifecycle, including usage restrictions, backup and recovery, retention, and permanent deletion in accordance with defined security and compliance requirements.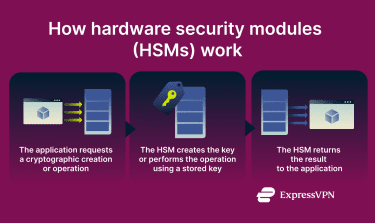
What HSMs are used for
Hardware security modules are typically used in environments where cryptographic keys must be strictly protected and operations must be isolated from general-purpose systems. Common use cases include:
- Transport Layer Security (TLS) offloading: Protecting private keys used for TLS termination so secure connections can be established without exposing keys to web servers.
- Digital certificates: Safeguarding certificate authority keys to ensure the trust and integrity of issued certificates.
- Blockchain operations: Securing private keys used to authorize and sign blockchain transactions.
- Digital signatures: Protecting signing keys used to verify the authenticity and integrity of documents, software, and messages.
- Card payments: Securing cryptographic keys used in payment processing, including PIN validation and transaction authorization.
Benefits of using an HSM
Organizations commonly use HSMs for the following reasons:
- Added security: Protects cryptographic keys within tamper-resistant hardware, reducing the risk of unauthorized access or key theft.
- Compliance requirements: Helps organizations meet regulatory requirements and security standards by enforcing strict key protection and usage controls.
- Improved performance: Offloads resource-intensive cryptographic operations from applications and servers to the HSM, improving overall system efficiency.
Security considerations and limitations
Because HSMs manage highly sensitive cryptographic keys, their security depends on correct configuration and access control. Improper setup, weak authorization policies, or overly broad administrative access can undermine the protections the HSM is intended to provide.
HSMs also introduce availability considerations. Hardware failure, misconfiguration, or loss of access to the device can disrupt cryptographic operations if backup, recovery, and redundancy mechanisms are not properly implemented. In addition, while HSMs protect keys from extraction, they don’t eliminate the need to secure surrounding systems, such as applications, networks, and management interfaces, which can still be targeted to misuse authorized access.
HSM vs. software-based key storage
| HSM | Software-based key storage | |
| Cryptographic operations | Performed by the HSM, reducing the processing load on the host system | Handled by the device’s CPU, which may affect performance |
| Encryption keys | Generated, stored, and used entirely within the HSM | Managed by the operating system or individual applications |
| Target users | Enterprise-grade organizations with high security or compliance needs | Consumers and small teams with basic security or compliance requirements |
Further reading
- Ultimate guide to IoT device security
- Security concerns in cloud computing and how to address them
- 7 fastest ways to level up your privacy


