Expressvpn Glossary
Security token
What is a security token?
A security token, also known as an authentication token, is a digital credential that proves a user’s identity to a website, app, or API. It’s issued when a user successfully authenticates themselves and is used as proof of their identity for future requests until it expires or they log out.
These tokens are typically signed by the server issuing them, meaning that their data hasn’t been tampered with. They can also be encrypted so outside parties can’t view their information.
How does a security token work?
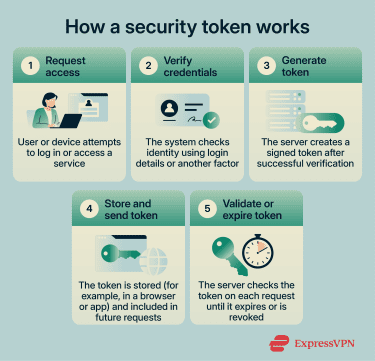
Security tokens generally work like this:
- Authentication request: The user enters login credentials.
- Verification: The server validates those credentials.
- Token generation: On success, the server generates and signs a token with a set expiration time.
- Token storage: The user’s device stores the token and sends it with future requests. The server verifies the token and grants access without another login.
- Token expiry: When the token expires or the user logs out, a new login is required to obtain a fresh token.
Types of security tokens
Security tokens come in several forms, depending on the use case:
- Session tokens: Reference server-side session data tied to a user’s authenticated session.
- Access and refresh token pairs: Access tokens grant short-term access to resources. Refresh tokens obtain new access tokens without forcing the user to log in again.
- API tokens: Identify applications or users when interacting with an API.
- Hardware tokens: Physical devices such as smart cards or key fobs used for identity verification.
- Software tokens: App-based tokens often used in multi-factor authentication (MFA).
Why is a security token important?
Security tokens reduce password exposure. Since credentials are only submitted during login, they’re not repeatedly transmitted with every request.
They also support least-privilege access. A token can contain claims that define what the holder is allowed to access, making it easier to limit permissions and reduce risk.
Where are security tokens used?
Websites and mobile apps use security tokens. API-driven systems also rely on tokens to authorize requests between services.
Authorization frameworks like OAuth use tokens extensively, too, enabling specific applications to interact on a user’s behalf without exposing login credentials.
Finally, enterprise identity providers use tokens to grant access to multiple internal systems through centralized authentication.
Risks and privacy concerns
There are some concerns about security tokens. For instance, if an attacker steals a valid token, they may be able to access an account until the token expires. In some cases, token theft can bypass MFA because the authentication step has already occurred.
Poor security practices when storing tokens can also leave them vulnerable to attackers. Tokens stored in browser local storage are vulnerable to theft via cross-site scripting (XSS) attacks.
Further reading
- What is OIDC? A complete guide to understanding the identity layer
- Passwordless authentication: What it is and why it matters
- What are passkeys? Here’s the next big sign-in method
- What is phishing-resistant MFA, and why does it matter?

