Expressvpn Glossary
TCP handshake

What is a TCP handshake?
Transmission Control Protocol (TCP) is a set of rules that computers follow to send data reliably over a network. It makes sure information arrives in the correct order and isn’t lost along the way. Most of the internet relies on TCP to function.
A TCP handshake is a brief setup process that happens before any data is sent. During this step, two devices confirm that they can reach each other and are ready to communicate.
How a TCP handshake works
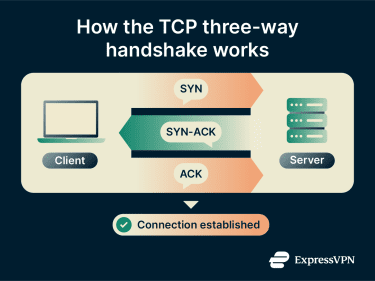
To start a TCP connection, two devices exchange a three-step set of messages to make sure they can communicate reliably. The device that initiates the connection is called the client, and the device that responds and provides the service or information the client requests is called the server.
This process is called the TCP handshake, also known as a three-way handshake for the three messages it uses:
- Synchronize (SYN): The client sends a SYN message to the server, indicating it wants to start a connection.
- Synchronize-acknowledge (SYN-ACK): The server replies with a SYN-ACK message to acknowledge the client’s request and indicate that it’s ready to connect.
- Acknowledge (ACK): The client sends a final ACK message to confirm the server’s response. Once this message is received, the connection is established, and data can be sent.
Why the TCP handshake is important
The TCP handshake is essential for making network connections work smoothly (including the internet). Here’s what it does:
- Prevents data loss: The handshake confirms that both devices are ready to send and receive data, reducing the chance that messages are lost when the connection starts.
- Synchronizes sequence numbers: Data is often sent in small pieces that may take different paths and arrive out of order. During the TCP handshake, both devices agree on sequence numbers that determine the order of these pieces, so they can be reassembled correctly at the destination.
- Manages network flow: The handshake helps devices coordinate how much data can be sent at once, preventing the network from becoming overloaded and keeping communication smooth.
Common issues and network risks
TCP handshakes can be disrupted due to misconfigurations or poor connections. They can also be exploited in various ways by cybercriminals. Here are the most common problems that occur:
- SYN flood attacks: Attackers can send a large number of fake connection requests (SYN messages) to a server, overwhelming it and preventing legitimate users from connecting.
- Misconfigured firewalls: If a firewall is accidentally set to block legitimate handshake messages, connections may fail or be delayed.
- Packet loss or latency: Network problems can cause handshake messages to be lost or delayed, which can interrupt connection attempts and slow down communication.
- SYN/ACK scanning: Attackers can send fake SYN or ACK messages to see how a network responds. These responses can reveal which systems, services, or firewall rules are in place, potentially exposing vulnerabilities.
Further reading
- What is TCP/IP and how does it work?
- TCP vs. UDP: Understanding the key differences and best use cases
- VPN protocols: OpenVPN (TCP vs. UDP)


