-
What are YouTube proxies and are they safe?
A YouTube proxy is a website designed to serve as an intermediary between a device and the streaming platform’s servers. This can bring a few benefits, but it also introduces privacy and security ri...
-

What is a VLAN? A complete guide to virtual LANs
A virtual local area network (VLAN) is a method of segmenting a single physical LAN into multiple separate networks through software. This guide covers how VLANs work, the possible benefits they bring...
-

Data sovereignty: What it is and compliance considerations
Every digital interaction generates data. Often, it moves across borders; a login request in Paris might be processed on servers in California and stored in Singapore. Given this constant global excha...
-

How to increase bandwidth when using a VPN: Complete guide
Bandwidth is an important but often misunderstood metric that affects overall internet speed. While many people think bandwidth refers to the speed of their internet connection, it’s actually a dist...
-

How to hide your IP address and protect your online privacy
Your online activity might not be as private as you think it is. The moment you connect to the internet, your device is assigned a unique Internet Protocol (IP) address. This is a digital identifier t...
-

Loopback address: What it is and how to use it
A loopback address is a way for a computer to talk to itself. Instead of being sent outward, data directed to a loopback address returns to the same device. This can be a useful tool for testing appli...
-
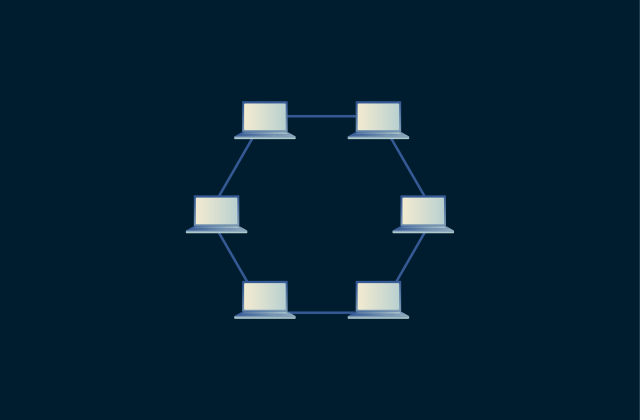
Network topology: Best practices for modern networks
A well-designed network starts with a clear understanding of its structure. Network topology is the blueprint of how devices and connections interact, and it plays a key role in determining a network�...
-

What is 128-bit encryption, and is it still secure in 2026?
128-bit encryption remains a cornerstone of online security, protecting everything from virtual private network (VPN) traffic to mobile apps. It’s widely used and has never been reported to have bee...
-
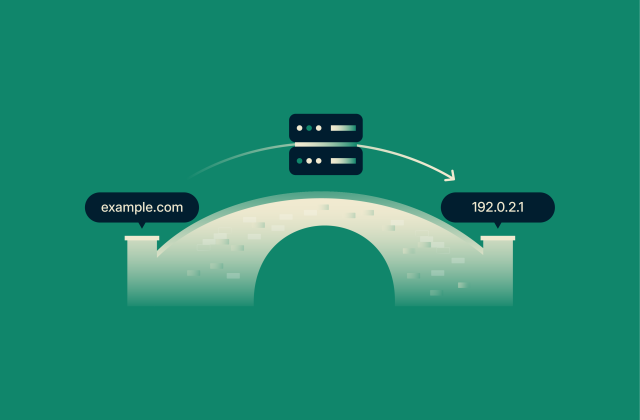
Nameserver: The complete guide to setup, management, and troubleshooting
Nameservers are essential for any functioning website or email domain. Without proper nameserver configuration, emails wouldn't reach their destinations, and visitors would encounter loading errors wh...
-

Connected but no internet access: Why it happens and how to fix it
Getting a message stating that you’re connected but have no internet access can be frustrating. If your network is fine, why won’t websites load? It’s often unclear what has caused this error me...
-
- No-Logs Policy
- Servers in 105 Countries
- Use on Multiple Devices
- High-Speed VPN
- Access Online Services Securely
- VPN for Gaming
- 30-Day Money-Back Guarantee
- Explore All Features
- About ExpressVPN
One subscription gives you access to a fast-growing suite of privacy and security tools that work seamlessly together to improve your digital life.
View all products - Download VPN
- Pricing
- VPN for Teams
- Products
-
ExpressVPN Industry-leading, ultra-fast VPN with secure servers in 105 countries.
-
ExpressMailGuard Private email relay service to protect your inbox and identity.
-
ExpressKeys Secure password management, multi-factor authentication, and more.
-
ExpressAI The first consumer AI powered by confidential computing for privacy-led intelligence.
-
Identity Defender Powerful suite of ID protection, monitoring, and data removal tools
Other products from the family behind ExpressVPN
-
- My Account


