Expressvpn Glossary
HTTPS proxy
What is an HTTPS proxy?
An HTTPS proxy is an intermediary server that forwards encrypted web traffic between a client and a destination website. It allows HTTPS requests to pass through a proxy while maintaining Transport Layer Security (TLS) protection between the client and the server.
Organizations and networks use HTTPS proxies to manage, monitor, or route web traffic without directly terminating the encrypted session in most cases.
How does an HTTPS proxy work?
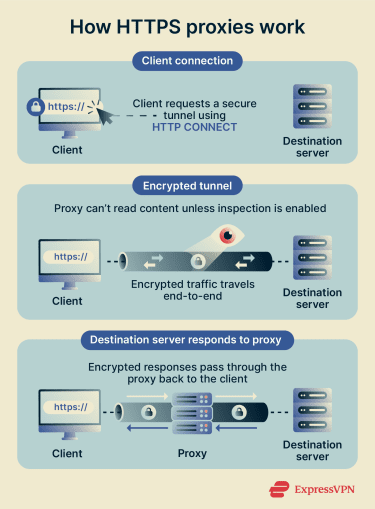 When a client accesses an HTTPS website through a proxy, the client first sends an HTTP CONNECT request to the proxy, asking it to establish a tunnel to the destination server.
When a client accesses an HTTPS website through a proxy, the client first sends an HTTP CONNECT request to the proxy, asking it to establish a tunnel to the destination server.
Once the tunnel is created, the client and the destination server perform a TLS handshake directly through the proxy. The proxy forwards encrypted packets between the two endpoints without decrypting them.
In environments where TLS inspection is enabled, the proxy temporarily decrypts and re-encrypts traffic using a trusted certificate authority (CA), allowing the traffic to be analyzed or filtered before it reaches the destination.
Types of HTTPS proxies
HTTPS proxies can be classified into several types, each with specific uses and behaviors:
- Forward HTTPS proxy: Used by clients to route outbound traffic through a secure intermediary, hiding the client’s IP from the destination and applying policies or filters.
- Reverse HTTPS proxy: Deployed by websites or services to manage incoming requests, often for load balancing, caching, or improving performance.
- Intercepting HTTPS proxy: Also called SSL/TLS inspection proxies, these sit between the client and server to temporarily decrypt traffic for monitoring, filtering, or security scanning.
Why is an HTTPS proxy important?
HTTPS proxies are a widely used element in computer networking. They help with:
- Applying content or ad filtering and blocking malware.
- Enforcing egress controls to prevent sensitive data from leaving a network.
- Supporting auditing and incident response through logging and monitoring.
- Distributing traffic across multiple servers, which lowers the burden on any single machine and ensures higher reliability.
Where are HTTPS proxies used?
HTTPS proxies are deployed in a wide range of contexts to enhance security, control, and operational flexibility. In enterprise networks and on managed endpoints, they monitor, filter, and secure outbound traffic while enforcing policies and logging activity for auditing and compliance. They can also be a component of zero‑trust network access (ZTNA) frameworks, where they regulate internet access, block threats, and control authenticated connections.
Beyond enterprises, HTTPS proxies are commonly used in educational institutions and library networks to enforce remote access. They also support software development and testing environments, enabling controlled proxy networks for automation, staging, and network simulation.
Security and privacy considerations
Despite their benefits, HTTPS proxies can introduce several risks. This includes:
- Logging private information: If a proxy’s CA certificate is manually trusted, decryption becomes possible. This risks exposing sensitive data to intermediaries, bypassing privacy protections that standard, non-intercepted HTTPS sessions would otherwise provide.
- Breaking end‑to‑end encryption (E2EE): Normally, a browser uses features like HTTP Strict Transport Security (HSTS) to block insecure connections. However, if the proxy’s CA is trusted, a browser won’t trigger a security warning. It assumes the connection is safe, even though the proxy has broken E2EE and is acting as an intermediary, intercepting everything sent and received.
- Malicious modification, injection, or unwanted content: Untrusted or malicious proxies can inject content, advertisements, or phishing material into traffic. This risk manifests if the proxy’s CA certificates are trusted, allowing the intermediary point to control and modify data.
- Risks from misconfiguration and protocol downgrades: Improperly configured intercepting proxies or weak certificate handling can introduce security vulnerabilities, such as enabling man‑in‑the‑middle (MITM) attacks or downgrading secure protocols.
Further reading
- What are anonymous proxies, and how do they work?
- What is a transparent proxy? A complete guide
- Port 443: What it is, how it works, and how to use it safely
- What is a VPN proxy and why do I need one??

